Phone and Laptop Seizures at Airports and Borders - Privacy Travel Guide
The world and its borders are slowly opening up after strict Covid lockdowns, and people are looking forward to travelling again. While this is great and fun, keep in mind that you might be subject to random searches and highly invasive and traumatic experiences.
"All my devices are completely encrypted, I don't need to read this article." I wish a statement like this would be true, dear reader. In reality, and depending on your location, you can get forced to submit your devices including passwords. This privacy travel guide offers you practical and realistic solutions on how to get past customs with your digital privacy intact.
TL;DR - Too long, didn't read
Border agents have the upper hand, you can be detained and your devices seized. Key disclosure laws make it legal to force you to surrender your passwords and biometric access. Back up your devices, use encrypted cloud storage, wipe and factory reset your device, create new travel accounts, restore your devices when you reach a safe network.
Expectations vs Reality
Common expectation: "I'm a lawful citizen and international traveller for pleasure or business. I have my rights, the encrypted devices I own are mine and without suspicion can't be taken away from me. The data on my devices can't be copied or stored without my approval. When shit hits the fan, I will just wipe all data off my device in front of the border agents."
While in reality, international travellers just got off a long and exhausting flight, sleep-deprived and confused. Moreover, you might be misinformed about the laws in the country you are about to enter, intimidated by the Border Force officers and unable to communicate properly due to language barriers. There is also a financial aspect of international travelling. You've already paid for your airline ticket and hotel room, and not cooperating with the border officers might result in you being forced to book an overpriced return ticket on very short notice. This adds tremendous financial stress to the situation.
All of this puts you in a bad position in the first place. You're tired, stress and confused, and you're facing trained and well-rested personnel with a lot of power over you in random searches.
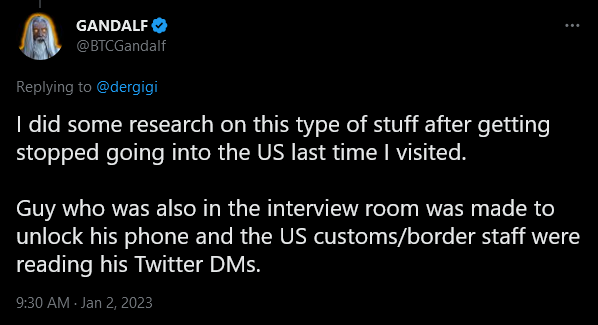
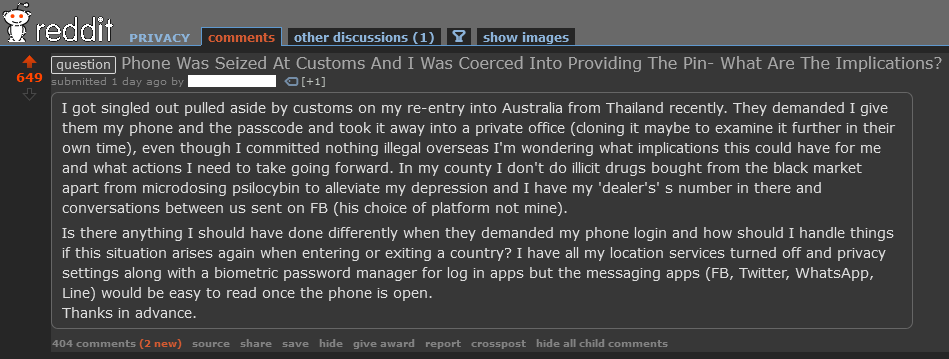
Traumatic and Highly Invasive Mockery of Privacy
A random data security search by Border Force officers can get you detained for an uncertain amount of time, all of your devices seized, forced to surrender passwords to bypass your encryption and your digital files inspected, copied and saved. In the US, data gets saved for 15 years in a database searchable by thousands of U.S. Customs and Border Protection employees without a warrant. The data includes messages, private photos, contacts, social media posts, medical and financial information, internet browsing history, call logs.
Even if you'd argue that "I have nothing to hide" it should be clear now that this is a highly invasive procedure and a mockery of your privacy. Keep in mind that these searches can be completely random and without suspicion of a crime.
Proper risk assessment is crucial in a situation like this. Stay respectful and calm, don't lie to border agents, physically obstruct them and document the procedure in a polite way. Ask for names of personnel, the agencies they work for and badge numbers. If you comply, the agents own your data. If you decline, the agents can seize your devices, deny entry in the country, question your permanent resident status and subject you to questioning and detention.
High Risk in the USA, China, Russia, Australia, UK and NZ
Several countries now created a legal foundation labelled as Key disclosure laws to compromise information privacy by requiring individuals to surrender cryptographic keys to law enforcement. Failure to disclose passwords to keys and result of several years in jail depending on the country. For a complete list of countries and more details, refer to this extensive Wikipedia article.
Simple and Easy Precautions
The bad news is, there is nothing to do in situations described before except to comply. The good news is, you don't have to be a computer expert to put some easy precautions in place before travelling.
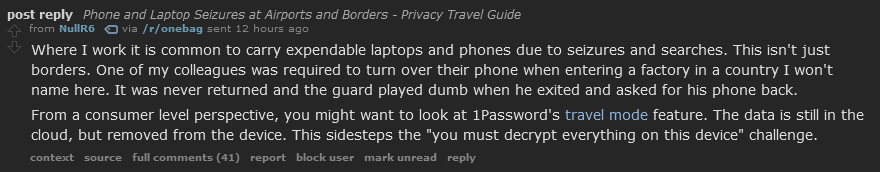
Instead of bringing your usual phone, tablet and laptop, bring devices that are set up and dedicated to travelling. These could be cheaper models like a Chromebook and a burner smartphone synced to a separate and non-sensitive account with minimum data and apps installed. Keep all confidential information out of these devices and make sure you're not logged into any cloud services that got access to them. This way you have access to a device with essential and necessary contacts, bookings, translation and Maps.
- Chromebooks provide basic computing, and they don't store a lot of data. Use them to sign in your dedicated travel account.
- Use on of our recommended best VPN provider when connecting to public Wi-Fi networks at airports, hotels etc.
- Install a private by default browser like LibreWolf or Brave.
- Set up a privacy email account for your new travel identity. Don't name the new account anything travelling related, though. That might raise suspicion. Pick something neutral that refers to an everyday use. Example: Use "johndoe99" instead of "johntravels23".
- Remember the account passwords for your travel accounts, don't store it in a password manager. You could come up with a long but easy to remember password like: "JohnnyTravelsToRome-2023-Alone".
- Add touristic pictures on your phone, so it doesn't appear to be empty and unused.
Once you arrive, consider installing privacy-respecting Apps
- Use alternative and private world maps and translation tools that are not tracking you.
- Pick an encrypted calendar and notebook to stay organized during your travels.
- Protect your files with encrypted cloud storage, photo storage, secure file encryption and use file sharing tools to sync your devices before and after your trip.
- Don't travel with social media apps installed on your phone. If you still have to use social media, use your browser to access it, and don't forget to log out and delete your browser history after every use.
- Do not install any personally identifying apps.
- Use an encrypted DNS resolver that is easy to set up and free to use.
- Don't forget to switch accounts on your Smartwatch and Band, too. Check out "Gadgetbride" in our Privacy Respecting Health & Fitness Apps category.
Make sure you don't have any social media accounts connected to your real name that is accessible by border agents. If they find those, they can require access to them, too.
"But my flagship phone got a really nice camera"
"I want to bring it to take nice pictures of my holiday. Also, my bookings, tickets and Maps are on that phone." I get that, it makes sense and takes away a lot of convenience otherwise. Create a complete backup of your phone, factory reset it, create a new account for travelling purposes. Follow all recommendations above.
This way you can still use your nice camera and manage your bookings while not bringing Gigabytes of private data to an international border. Once you get home again, copy your new pictures to the cloud, a laptop or PC and restore your old backup.
This whole process is especially easy on iOS devices, but doable as well for Android devices. While this might seem painful, it should be worth it to avoid ending up in a huge database and dealing with border agents.
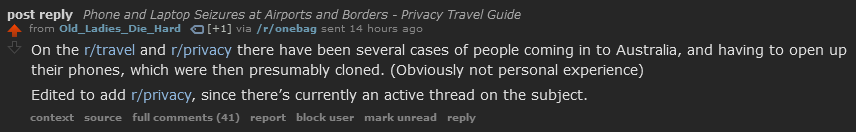
Data Sensitive Companies are Aware and Acting Already
Do you think this is paranoid and unnecessary? You should know that it is not uncommon for companies, that deal with sensitive data, to instruct employees to wipe all data off devices before getting on a plane and restore it on a secure network at the travel destination. They don't want sensitive customer data or company secrets in a central database, understandably.
Share this Privacy Travel Guide with your best friends and family
If you have found this article helpful, please share it with your best friends and family that are about to travel. It might save them some headache while crossing international borders. Stay safe and enjoy your trip! ❤️
Contact EFF for US Related Rights Violations
This only applies for US related travels, and if you feel border agents violated your rights by searching and sizing your devices and social media accounts: [email protected]. They also published an intensive "Digital Privacy at the U.S. Border: Protecting the Data On Your Devices and In the Cloud" report that is worth reading, it's also offered as a PDF download.
News and Related Guides
- Can Border Agents Search Your Electronic Devices? It’s Complicated. - aclu.org
- Why your phone and laptop can be seized at an international Australian airport - and there’s nothing you can do about it - 7news.com.au
- Sydney airport seizure of phone and laptop 'alarming', say privacy groups - theguardian.com
- A Guide to Getting Past Customs With Your Digital Privacy Intact - wired.com
- How to prevent customs agents from copying your phone’s content - washingtonpost.com