How DNS and IP requests can be used to track you and how to avoid it
DNS stands for “Domain Name System” and is a service used by your browser (and other apps) to find the IP addresses of a service. It is a huge “contact list” (phone book for older people) that works like asking it a name and it returns the number to call. Except it returns an IP instead
Every time your browser wants to access a certain service such as Google through www.google.com. Your Browser (Chrome or Firefox) will query a DNS service to find the IP addresses of the Google web servers.
Here is a video explaining DNS visually if you are already lost: https://www.youtube.com/watch?v=vrxwXXytEuI [Invidious]
Usually, the DNS service is provided by your ISP and automatically configured by the network you are connecting to. This DNS service could also be subject to data retention regulations or will just keep logs for other reasons (data collection for advertising purposes for instance). Therefore, this ISP will be capable of telling everything you did online just by looking at those logs which can, in turn, be provided to an adversary. Conveniently this is also the easiest way for many adversaries to apply censoring or parental control by using DNS blocking. The provided DNS servers will give you a different address (than their real one) for some websites (like redirecting thepiratebay.org to some government website). Such blocking is widely applied worldwide for certain sites.
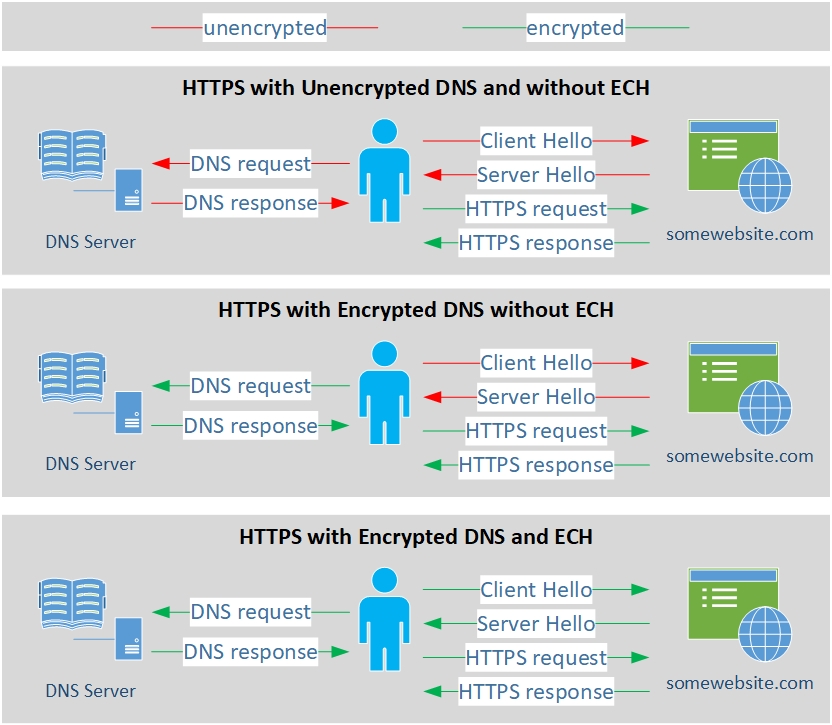
Using a private DNS service or your own DNS service would mitigate these issues, but the other problem is that most of those DNS requests are by default still sent in clear text (unencrypted) over the network. Even if you browse PornHub in an incognito Window, using HTTPS and using a private DNS service, chances are exceedingly high that your browser will send a clear text unencrypted DNS request to some DNS servers asking basically “So what’s the IP address of www.pornhub.com?”.
Because it is not encrypted, your ISP and/or any other adversary could still intercept (using a Man-in-the-middle attack) your request will know and possibly log what your IP was looking for. The same ISP can also tamper with the DNS responses even if you are using a private DNS. Rendering the use of a private DNS service useless.
As a bonus, many devices and apps will use hardcoded DNS servers bypassing any system setting you could set. This is for example the case with most (70%) Smart TVs and a large part (46%) of Game Consoles. For these devices, you will have to force them to stop using their hardcoded DNS service which could make them stop working properly.
A solution to this is to use encrypted DNS using DoH (DNS over HTTPS), DoT (DNS over TLS) with a private DNS server (this can be self-hosted locally with a solution like pi-hole, remotely hosted with a solution like nextdns.io or using the solutions provider by your VPN provider or the Tor network). This should prevent your ISP or some go-between from snooping on your requests … except it might not.
Small in-between Disclaimer: This guide does not necessarily endorse or recommends Cloudflare services even if it is mentioned several times in this section for technical understanding.
Unfortunately, the TLS protocol used in most HTTPS connections in most Browsers (Chrome/Brave among them) will leak the Domain Name again through SNI handshakes (this can be checked here at Cloudflare: https://www.cloudflare.com/ssl/encrypted-sni/ [Archive.org] ). As of the writing of this guide, only Firefox-based browsers supports ECH (Encrypted Client Hello previously known as eSNI) on some websites which will encrypt everything end to end (in addition to using a secure private DNS over TLS/HTTPS) and will allow you to hide your DNS requests from a third party. And this option is not enabled by default either so you will have to enable it yourself.
In addition to limited browser support, only Web Services and CDNs behind Cloudflare CDN support ECH/eSNI at this stage. This means that ECH and eSNI are not supported (as of the writing of this guide) by most mainstream platforms such as:
- Amazon (including AWS, Twitch…)
- Microsoft (including Azure, OneDrive, Outlook, Office 365…)
- Google (including Gmail, Google Cloud…)
- Apple (including iCloud, iMessage…)
- YouTube
- GitHub
Some countries like Russia and China might (unverified despite the articles) block ECH/eSNI handshakes at the network level to allow snooping and prevent bypassing censorship. Meaning you will not be able to establish an HTTPS connection with a service if you do not allow them to see what it was.
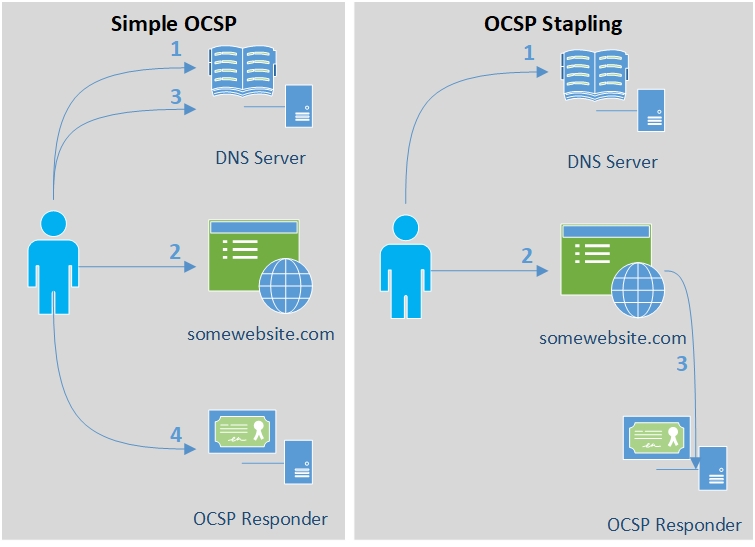
The issues do not end here. Part of the HTTPS TLS validation is called OCSP and this protocol used by Firefox-based browsers will leak metadata in the form of the serial number of the certificate of the website you are visiting. An adversary can then easily find which website you are visiting by matching the certificate number. This issue can be mitigated by using OCSP stapling. Unfortunately, this is enabled but not enforced by default in Firefox/Tor Browser. But the website you are visiting must also be supporting it and not all do. Chromium-based browsers on the other hand use a different system called CRLSets which is arguably better.
Here is a list of how various browsers behave with OCSP: https://www.ssl.com/blogs/how-do-browsers-handle-revoked-ssl-tls-certificates/ [Archive.org]
Here is an illustration of the issue you could encounter on Firefox-based browsers:
Finally, even if you use a custom encrypted DNS server (DoH or DoT) with ECH/eSNI support and OCSP stapling, it might still not be enough as traffic analysis studies have shown it is still possible to reliably fingerprint and block unwanted requests. Only DNS over Tor was able to show efficient DNS Privacy in recent studies but even that can still be defeated by other means (see Your Anonymized Tor/VPN traffic).
One could also decide to use a Tor Hidden DNS Service or ODoH (Oblivious DNS over HTTPS) to further increase privacy/anonymity but unfortunately, as far as I know, these methods are only provided by Cloudflare as of this writing (https://blog.cloudflare.com/welcome-hidden-resolver/ [Archive.org], https://blog.cloudflare.com/oblivious-dns/ [Archive.org]). These are workable and reasonably secure technical options but there is also a moral choice if you want to use Cloudflare or not (despite the risk posed by some researchers).
Lastly, there is also this new possibility called DoHoT which stands for DNS over HTTPS over Tor which could also further increase your privacy/anonymity and which you could consider if you are more skilled with Linux. See https://github.com/alecmuffett/dohot [Archive.org]. This guide will not help you with this one at this stage, but it might be coming soon.
Here is an illustration showing the current state of DNS and HTTPS privacy based on my current knowledge.
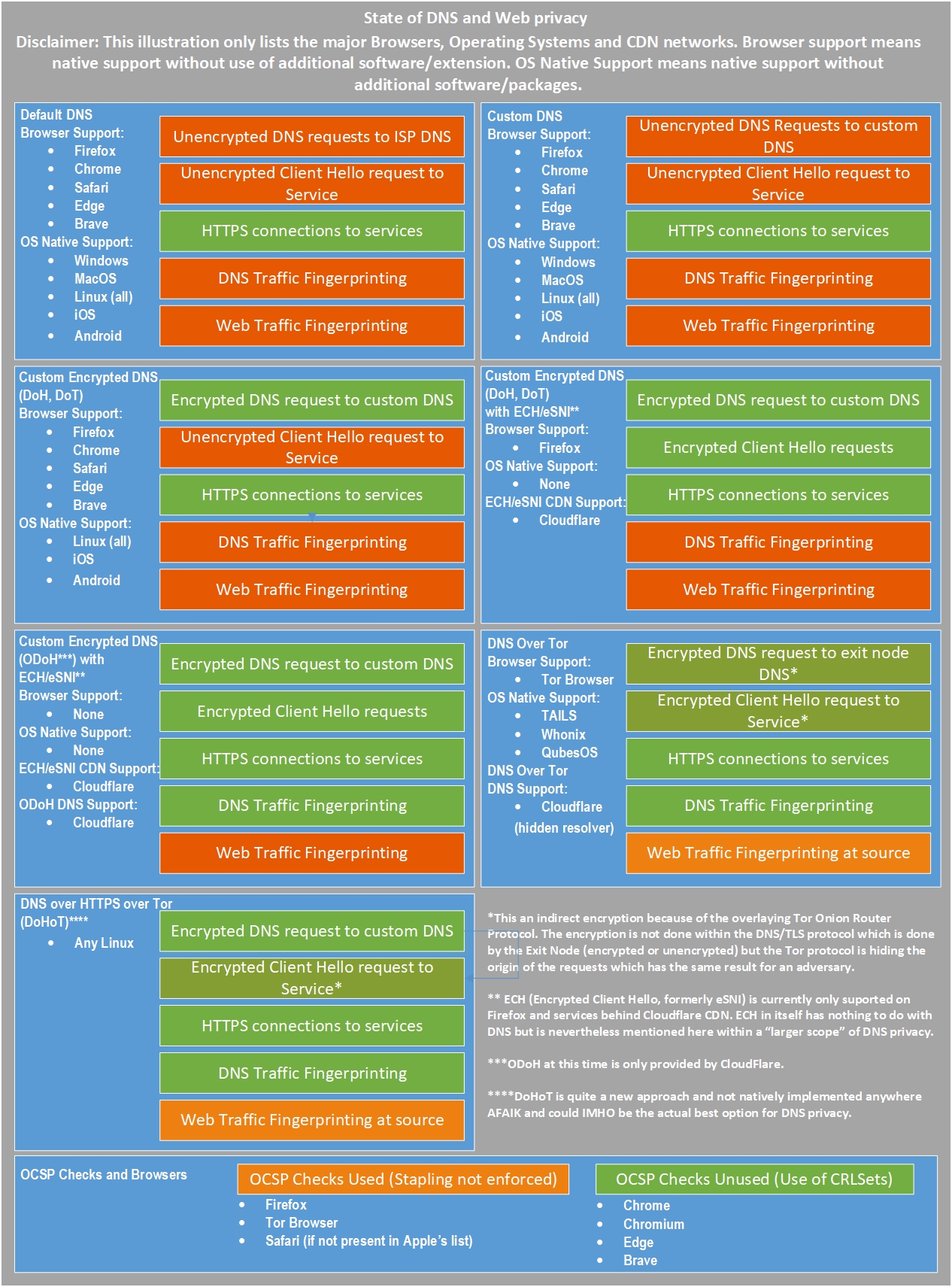
As for your normal daily use (non-sensitive), remember that only Firefox-based browsers support ECH (formerly eSNI) so far and that it is only useful with websites hosted behind Cloudflare CDN at this stage. If you prefer a Chrome-based version (which is understandable for some due to some better-integrated features like on-the-fly Translation), then I would recommend the use of Brave instead which supports all Chrome extensions and offers much better privacy than Chrome.
But the story does not stop there right. Now because after all this, even if you encrypt your DNS and use all possible mitigations. Simple IP requests to any server will probably allow an adversary to still detect which site you are visiting. And this is simply because the majority of websites have unique IPs tied to them as explained here: https://blog.apnic.net/2019/08/23/what-can-you-learn-from-an-ip-address/ [Archive.org]. This means that an adversary can create a dataset of known websites for instance including their IPs and then match this dataset against the IP you ask for. In most cases, this will result in a correct guess of the website you are visiting. This means that despite OCSP stapling, despite ECH/eSNI, despite using Encrypted DNS … An adversary can still guess the website you are visiting anyway.
Therefore, to mitigate all these issues (as much as possible and as best as we can), this guide will later recommend two solutions: Using Tor and a virtualized (See Virtualization) multi-layered solution of VPN over Tor solution (DNS over VPN over Tor or DNS over TOR). Other options will also be explained (Tor over VPN, VPN only, No Tor/VPN) but are less recommended.
Source: The Hitchhiker’s Guide to Online Anonymity, written by AnonyPla © CC BY-NC 4.0
